- Active Directory Enable Pin Login
- Active Directory Service Account
- View Active Directory Logins
- Active Directory Pin Login Page
- Active Directory Pin Login Yahoo
Active Directory If your laptop/desktop (Windows 8.1 or later) or your Windows Server (2012 and later) is joined to a classic Active Directory, you can use a YubiKey for login using the Smart Card functionality. Learn more about smart card login. Using LDAP/Active Directory with PIN based authentication. Ask Question Asked 6 years, 5 months ago. Windows login, Corporate Intranet.
Once the PIN is accepted, the user has access to all local and network resources to which the user's Active Directory account has been granted permissions. The techniques covered here only apply to using smart card logons on computers that are attached to a domain.
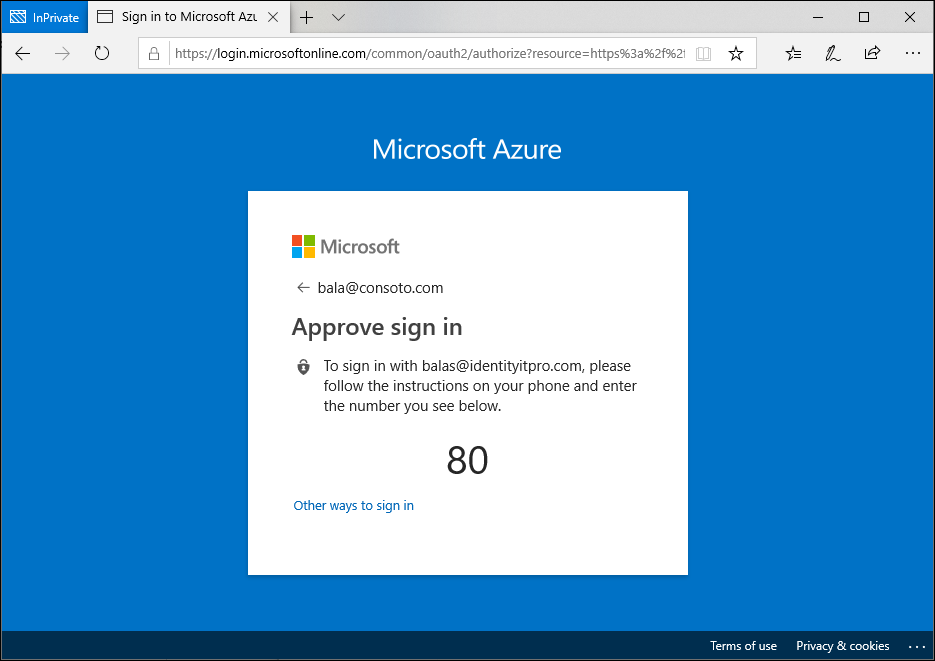
- Azure Active Directory https. When joining Windows 10 devices to Azure AD during the OOBE process we are getting prompted (forced) to create PIN. I have tried to.
- Change Password Using Active Directory. It is related to network directory, which performed from Windows Server Active Directory or PowerShell cmdlets. Type dsa.msc on Windows run to open active directory. Then find and change the password of a user. Change Password Using Active Directory.
This article provides some guidelines for enabling smart card logon with third-party certification authorities.
Original product version: Windows Server 2012 R2, Windows 10 - all editions
Original KB number: 281245
Summary
You can enable a smart card logon process with Microsoft Windows 2000 and a non-Microsoft certification authority (CA) by following the guidelines in this article. Limited support for this configuration is described later in this article.
Active Directory Enable Pin Login
More information
Requirements
Smart Card Authentication to Active Directory requires that Smartcard workstations, Active Directory, and Active Directory domain controllers be configured properly. Active Directory must trust a certification authority to authenticate users based on certificates from that CA. Both Smartcard workstations and domain controllers must be configured with correctly configured certificates.
As with any PKI implementation, all parties must trust the Root CA to which the issuing CA chains. Both the domain controllers and the smartcard workstations trust this root.
Active Directory Service Account
Active Directory and domain controller configuration
- Required: Active Directory must have the third-party issuing CA in the NTAuth store to authenticate users to active directory.
- Required: Domain controllers must be configured with a domain controller certificate to authenticate smartcard users.
- Optional: Active Directory can be configured to distribute the third-party root CA to the trusted root CA store of all domain members using the Group Policy.
Smartcard certificate and workstation requirements
- Required: All of the smartcard requirements outlined in the 'Configuration Instructions' section must be met, including the text formatting of the fields. Smartcard authentication fails if they are not met.
- Required: The smartcard and private key must be installed on the smartcard.
Configuration instructions

Export or download the third-party root certificate. How to obtaining the party root certificate varies by vendor. The certificate must be in Base64 Encoded X.509 format.
Add the third-party root CA to the trusted roots in an Active Directory Group Policy object. To configure Group Policy in the Windows 2000 domain to distribute the third-party CA to the trusted root store of all domain computers:
- Click Start, point to Programs, point to Administrative Tools, and then click Active Directory Users and Computers.
- In the left pane, locate the domain in which the policy you want to edit is applied.
- Right-click the domain, and then click Properties.
- Click the Group Policy tab.
- Click the Default Domain Policy Group Policy object, and then click Edit. A new window opens.
- In the left pane, expand the following items:
- Computer Configuration
- Windows Settings
- Security Settings
- Public Key Policy
- Right-click Trusted Root Certification Authorities.
- Select All Tasks, and then click Import.
- Follow the instructions in the wizard to import the certificate.
- Click OK.
- Close the Group Policy window.
Add the third party issuing the CA to the NTAuth store in Active Directory.
The smart card logon certificate must be issued from a CA that is in the NTAuth store. By default, Microsoft Enterprise CAs are added to the NTAuth store.
If the CA that issued the smart card logon certificate or the domain controller certificates is not properly posted in the NTAuth store, the smart card logon process does not work. The corresponding answer is 'Unable to verify the credentials'.
The NTAuth store is located in the Configuration container for the forest. For example, a sample location is as follows: LDAP://server1.name.com/CN=NTAuthCertificates,CN=Public Key Services,CN=Services,CN=Configuration,DC=name,DC=com
Work at a faster clip. With its modern Metal engine, Final Cut Pro allows you to edit more complex. It is not upgradeable, but all Macs on the market meet FCP's minimum requirements now. OS X 10.6 and beyond, running on an Intel CPU Mac, is 64-bit which allows for applications to access multiple CPUs at once. Thus, the more CPU cores the more power you'll have. FCP takes advantage of this. Send your iMovie for iOS project directly to Final Cut Pro for advanced editing, audio work, and finishing Generate proxy media in custom frame sizes from 12.5% to 100% of the original in ProRes Proxy or H.264 Automatically display the most useful functions for your task using the Touch Bar on MacBook Pro. Restart your Mac. Restarting your computer resets Final Cut Pro X-related system resources. Final Cut Pro revolutionizes post-production with 360° video, HDR, and advanced tools for color correction. Get a free trial of the latest version of Final Cut Pro for your Mac. Looking for Final Cut Pro? Minimum System Requirements. See minimum system requirements for Final Cut Pro. Final cut pro mac catalina.
By default, this store is created when you install a Microsoft Enterprise CA. The object can also be created manually by using ADSIedit.msc in the Windows 2000 Support tools or by using LDIFDE. For more information, click the following article number to view the article in the Microsoft Knowledge Base:
295663 How to import third-party certification authority (CA) certificates into the Enterprise NTAuth store
The relevant attribute is cACertificate, which is an octet String, multiple-valued list of ASN-encoded certificates.
After you put the third-party CA in the NTAuth store, Domain-based Group Policy places a registry key (a thumbprint of the certificate) in the following location on all computers in the domain:
HKEY_LOCAL_MACHINESoftwareMicrosoftEnterpriseCertificatesNTAuthCertificates
It is refreshed every eight hours on workstations (the typical Group Policy pulse interval).
Request and install a domain controller certificate on the domain controller(s). Each domain controller that is going to authenticate smartcard users must have a domain controller certificate.
If you install a Microsoft Enterprise CA in an Active Directory forest, all domain controllers automatically enroll for a domain controller certificate. For more information about requirements for domain controller certificates from a third-party CA, click the following article number to view the article in the Microsoft Knowledge Base:
291010 Requirements for domain controller certificates from a third-party CA
Note
The domain controller certificate is used for Secure Sockets Layer (SSL) authentication, Simple Mail Transfer Protocol (SMTP) encryption, Remote Procedure Call (RPC) signing, and the smart card logon process. Using a non-Microsoft CA to issue a certificate to a domain controller may cause unexpected behavior or unsupported results. An improperly formatted certificate or a certificate with the subject name absent may cause these or other capabilities to stop responding.
Request a smart card certificate from the third-party CA.
Enroll for a certificate from the third-party CA that meets the stated requirements. The method for enrollment varies by the CA vendor.
The smart card certificate has specific format requirements: Malankara catholic wedding songs lyrics.
- The CRL Distribution Point (CDP) location (where CRL is the Certification Revocation List) must be populated, online, and available. For example:
[1]CRL Distribution Point
Distribution Point Name:
Full Name:
URL=https://server1.name.com/CertEnroll/caname.crlKey Usage = Digital Signature
Basic Constraints [Subject Type=End Entity, Path Length Constraint=None] (Optional)
Enhanced Key Usage =
- Client Authentication (1.3.6.1.5.5.7.3.2)
(The client authentication OID) is only required if a certificate is used for SSL authentication.) - Smart Card Logon (1.3.6.1.4.1.311.20.2.2)
- Client Authentication (1.3.6.1.5.5.7.3.2)
Subject Alternative Name = Other Name: Principal Name= (UPN). For example:
UPN = user1@name.com
The UPN OtherName OID is: '1.3.6.1.4.1.311.20.2.3'
The UPN OtherName value: Must be ASN1-encoded UTF8 stringSubject = Distinguished name of user. This field is a mandatory extension, but the population of this field is optional.
There are two predefined types of private keys. These keys are Signature Only(AT_SIGNATURE) and Key Exchange(AT_KEYEXCHANGE). Smartcard logon certificates must have a Key Exchange(AT_KEYEXCHANGE) private key type in order for smartcard logon to function correctly.
Install smartcard drivers and software to the smartcard workstation.
Make sure that the appropriate smartcard reader device and driver software are installed on the smartcard workstation. It varies by smartcard reader vendor.
Install the third-party smartcard certificate to the smartcard workstation.
If the smartcard was not already put into the smartcard user's personal store in the enrollment process in step 4, then you must import the certificate into the user's personal store. To do so:
Open the Microsoft Management Console (MMC) that contains the Certificates snap-in.
In the console tree, under Personal, click Certificates.
On the All Tasks menu, click Import to start the Certificate Import Wizard.
Click the file that contains the certificates that you are importing.
Note
If the file that contains the certificates is a Personal Information Exchange (PKCS #12) file, type the password that you used to encrypt the private key, click to select the appropriate check box if you want the private key to be exportable, and then turn on strong private key protection (if you want to use this feature).
Note
To turn on strong private key protection, you must use the Logical Certificate Stores view mode.
Select the option to automatically put the certificate in a certificate store based on the type of certificate.
Install the third-party smartcard certificate onto the smartcard. This installation varies according to Cryptographic Service Provider (CSP) and by smartcard vendor. See the vendor's documentations for instructions.
Log on to the workstation with the smartcard.
Possible issues
During smartcard logon, the most common error message seen is:
The system could not log you on. Your credentials could not be verified.
This message is a generic error and can be the result of one or more of below issues.
Certificate and configuration problems
The domain controller has no domain controller certificate.
The SubjAltName field of the smartcard certificate is badly formatted. If the information in the SubjAltName field appears as Hexadecimal / ASCII raw data, the text formatting is not ASN1 / UTF-8.
The domain controller has an otherwise malformed or incomplete certificate.
For each of the following conditions, you must request a new valid domain controller certificate. If your valid domain controller certificate has expired, you may renew the domain controller certificate, but this process is more complex and typically more difficult than if you request a new domain controller certificate.
- The domain controller certificate has expired.
- The domain controller has an untrusted certificate. If the NTAuth store does not contain the certification authority (CA) certificate of the domain controller certificate's issuing CA, you must add it to the NTAuth store or obtain a DC certificate from an issuing CA whose certificate resides in the NTAuth store.
If the domain controllers or smartcard workstations do not trust the Root CA to which the domain controller's certificate chains, then you must configure those computers to trust that Root CA.
The smartcard has an untrusted certificate. If the NTAuth store does not contain the CA certificate of the smartcard certificate's issuing CA, you must add it to the NTAuth store or obtain a smartcard certificate from an issuing CA whose certificate resides in the NTAuth store.
If the domain controllers or smartcard workstations do not trust the Root CA to which the user's smartcard certificate chains, then you must configure those computers to trust that Root CA.
The certificate of the smart card is not installed in the user's store on the workstation. The certificate that is stored on the smartcard must reside on the smartcard workstation in the profile of the user who is logging on with the smart card.
Note
You do not have to store the private key in the user's profile on the workstation. It is only required to be stored on the smartcard.
The correct smartcard certificate or private key is not installed on the smartcard. The valid smartcard certificate must be installed on the smartcard with the private key and the certificate must match a certificate stored in the smartcard user's profile on the smartcard workstation.
The certificate of the smart card cannot be retrieved from the smartcard reader. It can be a problem with the smartcard reader hardware or the smartcard reader's driver software. Verify that you can use the smartcard reader vendor's software to view the certificate and the private key on the smartcard.
The smartcard certificate has expired.
No User Principal Name (UPN) is available in the SubjAltName extension of the smartcard certificate.
The UPN in SubjAltName field of the smartcard certificate is badly formatted. If the information in the SubjAltName appears as Hexadecimal / ASCII raw data, the text formatting is not ASN1 / UTF-8.
The smartcard has an otherwise malformed or incomplete certificate. For each of these conditions, you must request a new valid smartcard certificate and install it onto the smartcard and into the profile of the user on the smartcard workstation. The smartcard certificate must meet the requirements described earlier in this article, which include a correctly formatted UPN field in the SubjAltName field.
If your valid smartcard certificate has expired, you may also renew the smartcard certificate, which is more complex and difficult than requesting a new smartcard certificate.
The user does not have a UPN defined in their Active Directory user account. The user's account in the Active Directory must have a valid UPN in the userPrincipalName property of the smartcard user's Active Directory user account.
The UPN in the certificate does not match the UPN defined in the user's Active Directory user account. Correct the UPN in the smartcard user's Active Directory user account or reissue the smartcard certificate so that the UPN value in the SubjAltName field the matches the UPN in smartcard users' Active Directory user account. We recommend that the smart card UPN matches the userPrincipalName user account attribute for third-party CAs. However, if the UPN in the certificate is the 'implicit UPN' of the account (format samAccountName@domain_FQDN), the UPN does not have to match the userPrincipalName property explicitly.
Revocation checking problems
If the revocation checking fails when the domain controller validates the smart card logon certificate, the domain controller denies the logon. The domain controller may return the error message mentioned earlier or the following error message:
The system could not log you on. The smartcard certificate used for authentication was not trusted.
Note
Failing to find and download the Certificate Revocation List (CRL), an invalid CRL, a revoked certificate, and a revocation status of 'unknown' are all considered revocation failures.
The revocation check must succeed from both the client and the domain controller. Make sure the following are true:
Revocation checking is not turned off.
Revocation check for the built-in revocation providers cannot be turned off. If a custom installable revocation provider is installed, it must be turned on.
Every CA Certificate except the root CA in the certificate chain contains a valid CDP extension in the certificate.
The CRL has a Next Update field and the CRL is up to date. You can check that the CRL is online at the CDP and valid by downloading it from Internet Explorer. You should be able to download and view the CRL from any of the HyperText Transport Protocol (HTTP) or File Transfer Protocol (FTP) CDPs in Internet Explorer from both the smartcard workstation(s) and the domain controller(s).
Verify that each unique HTTP and FTP CDP that is used by a certificate in your enterprise is online and available.
To verify that a CRL is online and available from an FTP or HTTP CDP:
- To open the Certificate in question, double-click on the .cer file or double-click the certificate in the store.
- Click the Details tab, and select the CRL Distribution Point field.
- In the bottom pane, highlight the full FTP or HTTP Uniform Resource Locator (URL) and copy it.
- Open Internet Explorer and paste the URL into the Address bar.
- When you receive the prompt, select the option to Open the CRL.
- Make sure that there is a Next Update field in the CRL and the time in the Next Update field has not passed.

To download or verify that a Lightweight Directory Access Protocol (LDAP) CDP is valid, you must write a script or an application to download the CRL. After you download and open the CRL, make sure that there is a Next Update field in the CRL and the time in the Next Update field has not passed.
Support
Microsoft Product Support Services does not support the third-party CA smart card logon process if it is determined that one or more of the following items contributes to the problem:
- Improper certificate format.
- Certificate status or revocation status not available from the third-party CA.
- Certificate enrollment issues from a third-party CA.
- The third-party CA cannot publish to Active Directory.
- A third-party CSP.
Additional information
The client computer checks the domain controller's certificate. The local computer therefore downloads a CRL for the domain controller certificate into the CRL cache.
The offline logon process does not involve certificates, only cached credentials.
To force the NTAuth store to be immediately populated on a local computer instead of waiting for the next Group Policy propagation, run the following command to initiate a Group Policy update:
You can also dump out the smart card information in Windows Server 2003 and in Windows XP by using the Certutil.exe -scinfo command.
Applies to
- Windows 10
You can create a Group Policy or mobile device management (MDM) policy that will implement Windows Hello on devices running Windows 10.
Important
The Group Policy setting Turn on PIN sign-in does not apply to Windows Hello for Business. It still prevents or enables the creation of a convenience PIN for Windows 10, version 1507 and 1511.
Beginning in version 1607, Windows Hello as a convenience PIN is disabled by default on all domain-joined computers. To enable a convenience PIN for Windows 10, version 1607, enable the Group Policy setting Turn on convenience PIN sign-in.
Use PIN Complexity policy settings to manage PINs for Windows Hello for Business.

Export or download the third-party root certificate. How to obtaining the party root certificate varies by vendor. The certificate must be in Base64 Encoded X.509 format.
Add the third-party root CA to the trusted roots in an Active Directory Group Policy object. To configure Group Policy in the Windows 2000 domain to distribute the third-party CA to the trusted root store of all domain computers:
- Click Start, point to Programs, point to Administrative Tools, and then click Active Directory Users and Computers.
- In the left pane, locate the domain in which the policy you want to edit is applied.
- Right-click the domain, and then click Properties.
- Click the Group Policy tab.
- Click the Default Domain Policy Group Policy object, and then click Edit. A new window opens.
- In the left pane, expand the following items:
- Computer Configuration
- Windows Settings
- Security Settings
- Public Key Policy
- Right-click Trusted Root Certification Authorities.
- Select All Tasks, and then click Import.
- Follow the instructions in the wizard to import the certificate.
- Click OK.
- Close the Group Policy window.
Add the third party issuing the CA to the NTAuth store in Active Directory.
The smart card logon certificate must be issued from a CA that is in the NTAuth store. By default, Microsoft Enterprise CAs are added to the NTAuth store.
If the CA that issued the smart card logon certificate or the domain controller certificates is not properly posted in the NTAuth store, the smart card logon process does not work. The corresponding answer is 'Unable to verify the credentials'.
The NTAuth store is located in the Configuration container for the forest. For example, a sample location is as follows: LDAP://server1.name.com/CN=NTAuthCertificates,CN=Public Key Services,CN=Services,CN=Configuration,DC=name,DC=com
Work at a faster clip. With its modern Metal engine, Final Cut Pro allows you to edit more complex. It is not upgradeable, but all Macs on the market meet FCP's minimum requirements now. OS X 10.6 and beyond, running on an Intel CPU Mac, is 64-bit which allows for applications to access multiple CPUs at once. Thus, the more CPU cores the more power you'll have. FCP takes advantage of this. Send your iMovie for iOS project directly to Final Cut Pro for advanced editing, audio work, and finishing Generate proxy media in custom frame sizes from 12.5% to 100% of the original in ProRes Proxy or H.264 Automatically display the most useful functions for your task using the Touch Bar on MacBook Pro. Restart your Mac. Restarting your computer resets Final Cut Pro X-related system resources. Final Cut Pro revolutionizes post-production with 360° video, HDR, and advanced tools for color correction. Get a free trial of the latest version of Final Cut Pro for your Mac. Looking for Final Cut Pro? Minimum System Requirements. See minimum system requirements for Final Cut Pro. Final cut pro mac catalina.
By default, this store is created when you install a Microsoft Enterprise CA. The object can also be created manually by using ADSIedit.msc in the Windows 2000 Support tools or by using LDIFDE. For more information, click the following article number to view the article in the Microsoft Knowledge Base:
295663 How to import third-party certification authority (CA) certificates into the Enterprise NTAuth store
The relevant attribute is cACertificate, which is an octet String, multiple-valued list of ASN-encoded certificates.
After you put the third-party CA in the NTAuth store, Domain-based Group Policy places a registry key (a thumbprint of the certificate) in the following location on all computers in the domain:
HKEY_LOCAL_MACHINESoftwareMicrosoftEnterpriseCertificatesNTAuthCertificates
It is refreshed every eight hours on workstations (the typical Group Policy pulse interval).
Request and install a domain controller certificate on the domain controller(s). Each domain controller that is going to authenticate smartcard users must have a domain controller certificate.
If you install a Microsoft Enterprise CA in an Active Directory forest, all domain controllers automatically enroll for a domain controller certificate. For more information about requirements for domain controller certificates from a third-party CA, click the following article number to view the article in the Microsoft Knowledge Base:
291010 Requirements for domain controller certificates from a third-party CA
Note
The domain controller certificate is used for Secure Sockets Layer (SSL) authentication, Simple Mail Transfer Protocol (SMTP) encryption, Remote Procedure Call (RPC) signing, and the smart card logon process. Using a non-Microsoft CA to issue a certificate to a domain controller may cause unexpected behavior or unsupported results. An improperly formatted certificate or a certificate with the subject name absent may cause these or other capabilities to stop responding.
Request a smart card certificate from the third-party CA.
Enroll for a certificate from the third-party CA that meets the stated requirements. The method for enrollment varies by the CA vendor.
The smart card certificate has specific format requirements: Malankara catholic wedding songs lyrics.
- The CRL Distribution Point (CDP) location (where CRL is the Certification Revocation List) must be populated, online, and available. For example:
[1]CRL Distribution Point
Distribution Point Name:
Full Name:
URL=https://server1.name.com/CertEnroll/caname.crlKey Usage = Digital Signature
Basic Constraints [Subject Type=End Entity, Path Length Constraint=None] (Optional)
Enhanced Key Usage =
- Client Authentication (1.3.6.1.5.5.7.3.2)
(The client authentication OID) is only required if a certificate is used for SSL authentication.) - Smart Card Logon (1.3.6.1.4.1.311.20.2.2)
- Client Authentication (1.3.6.1.5.5.7.3.2)
Subject Alternative Name = Other Name: Principal Name= (UPN). For example:
UPN = user1@name.com
The UPN OtherName OID is: '1.3.6.1.4.1.311.20.2.3'
The UPN OtherName value: Must be ASN1-encoded UTF8 stringSubject = Distinguished name of user. This field is a mandatory extension, but the population of this field is optional.
There are two predefined types of private keys. These keys are Signature Only(AT_SIGNATURE) and Key Exchange(AT_KEYEXCHANGE). Smartcard logon certificates must have a Key Exchange(AT_KEYEXCHANGE) private key type in order for smartcard logon to function correctly.
Install smartcard drivers and software to the smartcard workstation.
Make sure that the appropriate smartcard reader device and driver software are installed on the smartcard workstation. It varies by smartcard reader vendor.
Install the third-party smartcard certificate to the smartcard workstation.
If the smartcard was not already put into the smartcard user's personal store in the enrollment process in step 4, then you must import the certificate into the user's personal store. To do so:
Open the Microsoft Management Console (MMC) that contains the Certificates snap-in.
In the console tree, under Personal, click Certificates.
On the All Tasks menu, click Import to start the Certificate Import Wizard.
Click the file that contains the certificates that you are importing.
Note
If the file that contains the certificates is a Personal Information Exchange (PKCS #12) file, type the password that you used to encrypt the private key, click to select the appropriate check box if you want the private key to be exportable, and then turn on strong private key protection (if you want to use this feature).
Note
To turn on strong private key protection, you must use the Logical Certificate Stores view mode.
Select the option to automatically put the certificate in a certificate store based on the type of certificate.
Install the third-party smartcard certificate onto the smartcard. This installation varies according to Cryptographic Service Provider (CSP) and by smartcard vendor. See the vendor's documentations for instructions.
Log on to the workstation with the smartcard.
Possible issues
During smartcard logon, the most common error message seen is:
The system could not log you on. Your credentials could not be verified.
This message is a generic error and can be the result of one or more of below issues.
Certificate and configuration problems
The domain controller has no domain controller certificate.
The SubjAltName field of the smartcard certificate is badly formatted. If the information in the SubjAltName field appears as Hexadecimal / ASCII raw data, the text formatting is not ASN1 / UTF-8.
The domain controller has an otherwise malformed or incomplete certificate.
For each of the following conditions, you must request a new valid domain controller certificate. If your valid domain controller certificate has expired, you may renew the domain controller certificate, but this process is more complex and typically more difficult than if you request a new domain controller certificate.
- The domain controller certificate has expired.
- The domain controller has an untrusted certificate. If the NTAuth store does not contain the certification authority (CA) certificate of the domain controller certificate's issuing CA, you must add it to the NTAuth store or obtain a DC certificate from an issuing CA whose certificate resides in the NTAuth store.
If the domain controllers or smartcard workstations do not trust the Root CA to which the domain controller's certificate chains, then you must configure those computers to trust that Root CA.
The smartcard has an untrusted certificate. If the NTAuth store does not contain the CA certificate of the smartcard certificate's issuing CA, you must add it to the NTAuth store or obtain a smartcard certificate from an issuing CA whose certificate resides in the NTAuth store.
If the domain controllers or smartcard workstations do not trust the Root CA to which the user's smartcard certificate chains, then you must configure those computers to trust that Root CA.
The certificate of the smart card is not installed in the user's store on the workstation. The certificate that is stored on the smartcard must reside on the smartcard workstation in the profile of the user who is logging on with the smart card.
Note
You do not have to store the private key in the user's profile on the workstation. It is only required to be stored on the smartcard.
The correct smartcard certificate or private key is not installed on the smartcard. The valid smartcard certificate must be installed on the smartcard with the private key and the certificate must match a certificate stored in the smartcard user's profile on the smartcard workstation.
The certificate of the smart card cannot be retrieved from the smartcard reader. It can be a problem with the smartcard reader hardware or the smartcard reader's driver software. Verify that you can use the smartcard reader vendor's software to view the certificate and the private key on the smartcard.
The smartcard certificate has expired.
No User Principal Name (UPN) is available in the SubjAltName extension of the smartcard certificate.
The UPN in SubjAltName field of the smartcard certificate is badly formatted. If the information in the SubjAltName appears as Hexadecimal / ASCII raw data, the text formatting is not ASN1 / UTF-8.
The smartcard has an otherwise malformed or incomplete certificate. For each of these conditions, you must request a new valid smartcard certificate and install it onto the smartcard and into the profile of the user on the smartcard workstation. The smartcard certificate must meet the requirements described earlier in this article, which include a correctly formatted UPN field in the SubjAltName field.
If your valid smartcard certificate has expired, you may also renew the smartcard certificate, which is more complex and difficult than requesting a new smartcard certificate.
The user does not have a UPN defined in their Active Directory user account. The user's account in the Active Directory must have a valid UPN in the userPrincipalName property of the smartcard user's Active Directory user account.
The UPN in the certificate does not match the UPN defined in the user's Active Directory user account. Correct the UPN in the smartcard user's Active Directory user account or reissue the smartcard certificate so that the UPN value in the SubjAltName field the matches the UPN in smartcard users' Active Directory user account. We recommend that the smart card UPN matches the userPrincipalName user account attribute for third-party CAs. However, if the UPN in the certificate is the 'implicit UPN' of the account (format samAccountName@domain_FQDN), the UPN does not have to match the userPrincipalName property explicitly.
Revocation checking problems
If the revocation checking fails when the domain controller validates the smart card logon certificate, the domain controller denies the logon. The domain controller may return the error message mentioned earlier or the following error message:
The system could not log you on. The smartcard certificate used for authentication was not trusted.
Note
Failing to find and download the Certificate Revocation List (CRL), an invalid CRL, a revoked certificate, and a revocation status of 'unknown' are all considered revocation failures.
The revocation check must succeed from both the client and the domain controller. Make sure the following are true:
Revocation checking is not turned off.
Revocation check for the built-in revocation providers cannot be turned off. If a custom installable revocation provider is installed, it must be turned on.
Every CA Certificate except the root CA in the certificate chain contains a valid CDP extension in the certificate.
The CRL has a Next Update field and the CRL is up to date. You can check that the CRL is online at the CDP and valid by downloading it from Internet Explorer. You should be able to download and view the CRL from any of the HyperText Transport Protocol (HTTP) or File Transfer Protocol (FTP) CDPs in Internet Explorer from both the smartcard workstation(s) and the domain controller(s).
Verify that each unique HTTP and FTP CDP that is used by a certificate in your enterprise is online and available.
To verify that a CRL is online and available from an FTP or HTTP CDP:
- To open the Certificate in question, double-click on the .cer file or double-click the certificate in the store.
- Click the Details tab, and select the CRL Distribution Point field.
- In the bottom pane, highlight the full FTP or HTTP Uniform Resource Locator (URL) and copy it.
- Open Internet Explorer and paste the URL into the Address bar.
- When you receive the prompt, select the option to Open the CRL.
- Make sure that there is a Next Update field in the CRL and the time in the Next Update field has not passed.
To download or verify that a Lightweight Directory Access Protocol (LDAP) CDP is valid, you must write a script or an application to download the CRL. After you download and open the CRL, make sure that there is a Next Update field in the CRL and the time in the Next Update field has not passed.
Support
Microsoft Product Support Services does not support the third-party CA smart card logon process if it is determined that one or more of the following items contributes to the problem:
- Improper certificate format.
- Certificate status or revocation status not available from the third-party CA.
- Certificate enrollment issues from a third-party CA.
- The third-party CA cannot publish to Active Directory.
- A third-party CSP.
Additional information
The client computer checks the domain controller's certificate. The local computer therefore downloads a CRL for the domain controller certificate into the CRL cache.
The offline logon process does not involve certificates, only cached credentials.
To force the NTAuth store to be immediately populated on a local computer instead of waiting for the next Group Policy propagation, run the following command to initiate a Group Policy update:
You can also dump out the smart card information in Windows Server 2003 and in Windows XP by using the Certutil.exe -scinfo command.
-->Applies to
- Windows 10
You can create a Group Policy or mobile device management (MDM) policy that will implement Windows Hello on devices running Windows 10.
Important
The Group Policy setting Turn on PIN sign-in does not apply to Windows Hello for Business. It still prevents or enables the creation of a convenience PIN for Windows 10, version 1507 and 1511.
Beginning in version 1607, Windows Hello as a convenience PIN is disabled by default on all domain-joined computers. To enable a convenience PIN for Windows 10, version 1607, enable the Group Policy setting Turn on convenience PIN sign-in.
Use PIN Complexity policy settings to manage PINs for Windows Hello for Business.
Group Policy settings for Windows Hello for Business
The following table lists the Group Policy settings that you can configure for Windows Hello use in your workplace. These policy settings are available in User configuration and Computer Configuration under Policies > Administrative Templates > Windows Components > Windows Hello for Business.
Note
Starting with Windows 10, version 1709, the location of the PIN complexity section of the Group Policy is: Computer Configuration > Administrative Templates > System > PIN Complexity.
| Policy | Scope | Options | |
|---|---|---|---|
| Use Windows Hello for Business | Computer or user | Not configured: Device does not provision Windows Hello for Business for any user. Enabled: Device provisions Windows Hello for Business using keys or certificates for all users. Disabled: Device does not provision Windows Hello for Business for any user. | |
| Use a hardware security device | Computer | Not configured: Windows Hello for Business will be provisioned using TPM if available, and will be provisioned using software if TPM is not available. Enabled: Windows Hello for Business will only be provisioned using TPM. This feature will provision Windows Hello for Business using TPM 1.2 unless the option to exclude them is explicitly set. Disabled: Windows Hello for Business will be provisioned using TPM if available, and will be provisioned using software if TPM is not available. | |
| Use certificate for on-premises authentication | Computer or user | Not configured: Windows Hello for Business enrolls a key that is used for on-premises authentication. Enabled: Windows Hello for Business enrolls a sign-in certificate using ADFS that is used for on-premises authentication. Disabled: Windows Hello for Business enrolls a key that is used for on-premises authentication. | |
| Use PIN recovery | Computer | Added in Windows 10, version 1703 Not configured: Windows Hello for Business does not create or store a PIN recovery secret. PIN reset does not use the Azure-based PIN recovery service. Enabled: Windows Hello for Business uses the Azure-based PIN recovery service for PIN reset. Disabled: Windows Hello for Business does not create or store a PIN recovery secret. PIN reset does not use the Azure-based PIN recovery service. For more information about using the PIN recovery service for PIN reset see Windows Hello for Business PIN Reset. | |
| Use biometrics | Computer | Not configured: Biometrics can be used as a gesture in place of a PIN. Enabled: Biometrics can be used as a gesture in place of a PIN. Disabled: Only a PIN can be used as a gesture. | |
| PIN Complexity | Require digits | Computer | Not configured: Users must include a digit in their PIN. Enabled: Users must include a digit in their PIN. Disabled: Users cannot use digits in their PIN. |
| Require lowercase letters | Computer | Not configured: Users cannot use lowercase letters in their PIN. Enabled: Users must include at least one lowercase letter in their PIN. Disabled: Users cannot use lowercase letters in their PIN. | |
| Maximum PIN length | Computer | Not configured: PIN length must be less than or equal to 127. Enabled: PIN length must be less than or equal to the number you specify. Disabled: PIN length must be less than or equal to 127. | |
| Minimum PIN length | Computer | Not configured: PIN length must be greater than or equal to 4. Enabled: PIN length must be greater than or equal to the number you specify. Disabled: PIN length must be greater than or equal to 4. | |
| Expiration | Computer | Not configured: PIN does not expire. Enabled: PIN can be set to expire after any number of days between 1 and 730, or PIN can be set to never expire by setting policy to 0. Disabled: PIN does not expire. | |
| History | Computer | Not configured: Previous PINs are not stored. Enabled: Specify the number of previous PINs that can be associated to a user account that can't be reused. Disabled: Previous PINs are not stored. | |
| Require special characters | Computer | Not configured: Users cannot include a special character in their PIN. Enabled: Users must include at least one special character in their PIN. Disabled: Users cannot include a special character in their PIN. | |
| Require uppercase letters | Computer | Not configured: Users cannot include an uppercase letter in their PIN. Enabled: Users must include at least one uppercase letter in their PIN. Disabled: Users cannot include an uppercase letter in their PIN. | |
| Phone Sign-in | Use Phone Sign-in | Computer | Not currently supported. |
MDM policy settings for Windows Hello for Business
The following table lists the MDM policy settings that you can configure for Windows Hello for Business use in your workplace. These MDM policy settings use the PassportForWork configuration service provider (CSP).
Important
Starting in Windows 10, version 1607, all devices only have one PIN associated with Windows Hello for Business. This means that any PIN on a device will be subject to the policies specified in the PassportForWork CSP. The values specified take precedence over any complexity rules set via Exchange ActiveSync (EAS) or the DeviceLock CSP.
| Policy | Scope | Default | Options | |
|---|---|---|---|---|
| UsePassportForWork | Device or user | True | True: Windows Hello for Business will be provisioned for all users on the device. False: Users will not be able to provision Windows Hello for Business. Note If Windows Hello for Business is enabled, and then the policy is changed to False, users who previously set up Windows Hello for Business can continue to use it, but will not be able to set up Windows Hello for Business on other devices. | |
| RequireSecurityDevice | Device or user | False | True: Windows Hello for Business will only be provisioned using TPM. False: Windows Hello for Business will be provisioned using TPM if available, and will be provisioned using software if TPM is not available. Nat failover with dual isp. | |
| ExcludeSecurityDevice | TPM12 | Device | False | Added in Windows 10, version 1703 True: TPM revision 1.2 modules will be disallowed from being used with Windows Hello for Business. False: TPM revision 1.2 modules will be allowed to be used with Windows Hello for Business. |
| EnablePinRecovery | Device or user | False | Added in Windows 10, version 1703 True: Windows Hello for Business uses the Azure-based PIN recovery service for PIN reset. False: Windows Hello for Business does not create or store a PIN recovery secret. PIN reset does not use the Azure-based PIN recovery service. For more information about using the PIN recovery service for PIN reset see Windows Hello for Business PIN Reset. | |
| Biometrics | UseBiometrics | Device | False | True: Biometrics can be used as a gesture in place of a PIN for domain sign-in. False: Only a PIN can be used as a gesture for domain sign-in. |
FacialFeaturesUser EnhancedAntiSpoofing | Device | Not configured | Not configured: users can choose whether to turn on enhanced anti-spoofing. True: Enhanced anti-spoofing is required on devices which support it. False: Users cannot turn on enhanced anti-spoofing. | |
| PINComplexity | ||||
| Digits | Device or user | 1 | 0: Digits are allowed. 1: At least one digit is required. 2: Digits are not allowed. | |
| Lowercase letters | Device or user | 2 | 0: Lowercase letters are allowed. 1: At least one lowercase letter is required. 2: Lowercase letters are not allowed. | |
| Special characters | Device or user | 2 | 0: Special characters are allowed. 1: At least one special character is required. 2: Special characters are not allowed. | |
| Uppercase letters | Device or user | 2 | 0: Uppercase letters are allowed. 1: At least one uppercase letter is required. 2: Uppercase letters are not allowed. | |
| Maximum PIN length | Device or user | 127 | Maximum length that can be set is 127. Maximum length cannot be less than minimum setting. | |
| Minimum PIN length | Device or user | 4 | Minimum length that can be set is 4. Minimum length cannot be greater than maximum setting. | |
| Expiration | Device or user | 0 | Integer value specifies the period of time (in days) that a PIN can be used before the system requires the user to change it. The largest number you can configure for this policy setting is 730. The lowest number you can configure for this policy setting is 0. If this policy is set to 0, then the user's PIN will never expire. | |
| History | Device or user | 0 | Integer value that specifies the number of past PINs that can be associated to a user account that can't be reused. The largest number you can configure for this policy setting is 50. The lowest number you can configure for this policy setting is 0. If this policy is set to 0, then storage of previous PINs is not required. | |
| Remote | UseRemotePassport | Device or user | False | Not currently supported. |
View Active Directory Logins
Note
In Windows 10, version 1709 and later, if policy is not configured to explicitly require letters or special characters, users can optionally set an alphanumeric PIN. Prior to version 1709 the user is required to set a numeric PIN.
Policy conflicts from multiple policy sources
Windows Hello for Business is designed to be managed by Group Policy or MDM but not a combination of both. If policies are set from both sources it can result in a mixed result of what is actually enforced for a user or device.
Policies for Windows Hello for Business are enforced using the following hierarchy: User Group Policy > Computer Group Policy > User MDM > Device MDM > Device Lock policy. All PIN complexity policies are grouped together and enforced from a single policy source.
Use a hardware security device and RequireSecurityDevice enforcement are also grouped together with PIN complexity policy. Conflict resolution for other Windows Hello for Business policies is enforced on a per policy basis.
Note
Windows Hello for Business policy conflict resolution logic does not respect the ControlPolicyConflict/MDMWinsOverGP policy in the Policy CSP.
Examples
The following are configured using computer Group Policy:
- Use Windows Hello for Business - Enabled
- User certificate for on-premises authentication - Enabled
- Require digits - Enabled
- Minimum PIN length - 6
The following are configured using device MDM Policy:
- UsePassportForWork - Disabled
- UseCertificateForOnPremAuth - Disabled
- MinimumPINLength - 8
- Digits - 1
- LowercaseLetters - 1
- SpecialCharacters - 1
Active Directory Pin Login Page
Enforced policy set:
- Use Windows Hello for Business - Enabled
- Use certificate for on-premises authentication - Enabled
- Require digits - Enabled
- Minimum PIN length - 6d
How to use Windows Hello for Business with Azure Active Directory
There are three scenarios for using Windows Hello for Business in Azure AD–only organizations:
- Organizations that use the version of Azure AD included with Office 365. For these organizations, no additional work is necessary. When Windows 10 was released to general availability, Microsoft changed the behavior of the Office 365 Azure AD stack. When a user selects the option to join a work or school network, the device is automatically joined to the Office 365 tenant's directory partition, a certificate is issued for the device, and it becomes eligible for Office 365 MDM if the tenant has subscribed to that feature. In addition, the user will be prompted to log on and, if MFA is enabled, to enter an MFA proof that Azure AD sends to his or her phone.
- Organizations that use the free tier of Azure AD. For these organizations, Microsoft has not enabled automatic domain join to Azure AD. Organizations that have signed up for the free tier have the option to enable or disable this feature, so automatic domain join won't be enabled unless and until the organization's administrators decide to enable it. When that feature is enabled, devices that join the Azure AD domain by using the Connect to work or school dialog box will be automatically registered with Windows Hello for Business support, but previously joined devices will not be registered.
- Organizations that have subscribed to Azure AD Premium have access to the full set of Azure AD MDM features. These features include controls to manage Windows Hello for Business. You can set policies to disable or force the use of Windows Hello for Business, require the use of a TPM, and control the length and strength of PINs set on the device.
If you want to use Windows Hello for Business with certificates, you'll need a device registration system. That means that you set up Configuration Manager, Microsoft Intune, or a compatible non-Microsoft MDM system and enable it to enroll devices. This is a prerequisite step to use Windows Hello for Business with certificates, no matter the IDP, because the enrollment system is responsible for provisioning the devices with the necessary certificates.
